Ransomware review: June 2023
Threat Intelligence Team
Threat Intelligence Team
This article is based on research by Marcelo Rivero, Malwarebytes’ ransomware specialist, who monitors information published by ransomware gangs on their Dark Web sites. In this report, “known attacks” are those where the victim didn’t pay a ransom. This provides the best overall picture of ransomware activity, but the true number of attacks is far higher.
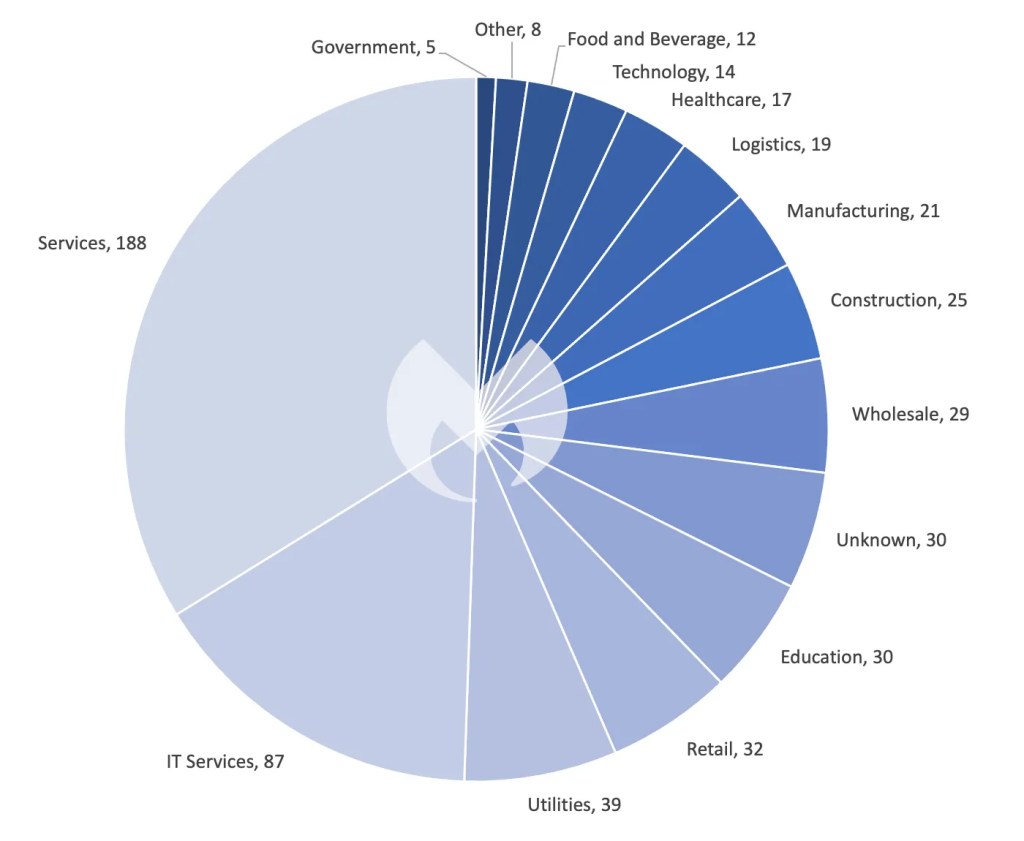
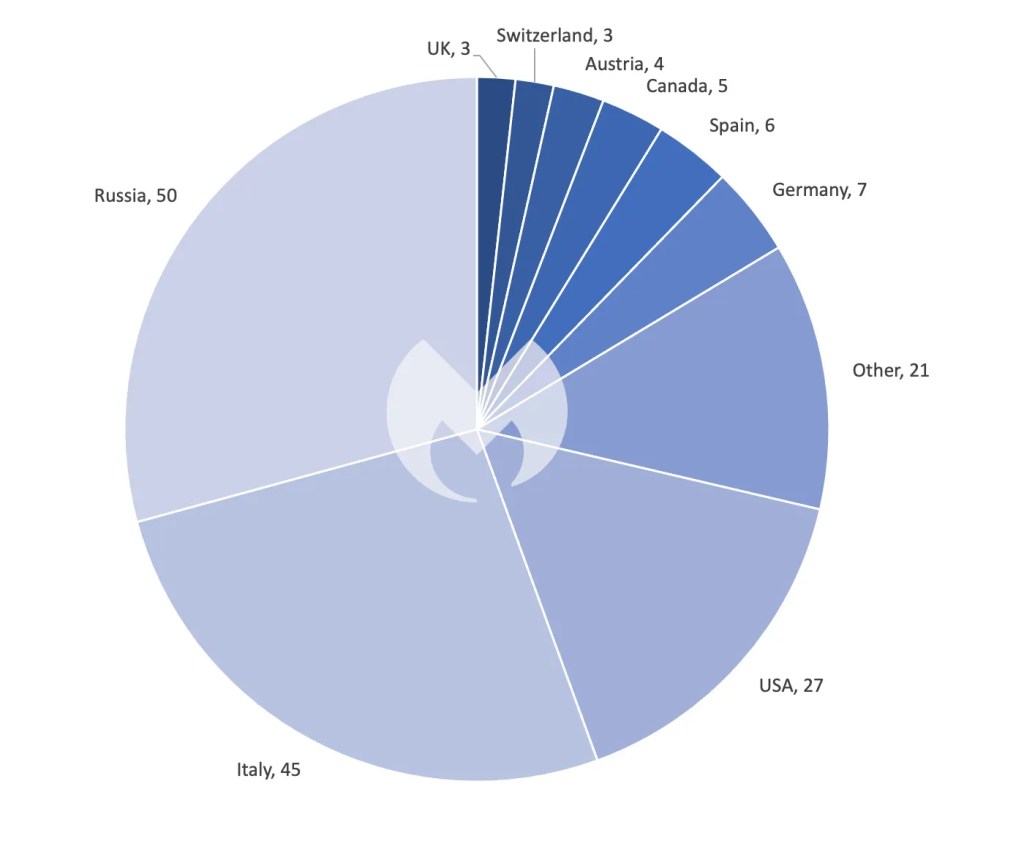
In May, Lockbit, usually the reigning king of ransomware, found a fierce competitor in MalasLocker. Last month also witnessed a record number of 556 reported ransomware victims, the unusual emergence of Italy and Russia as major targets, and a significant rise in attacks on the education sector.
Let’s jump right in with MalasLocker, who burst onto the scene last month with 171 total victims—beating out LockBit (76) by almost 100 known attacks.
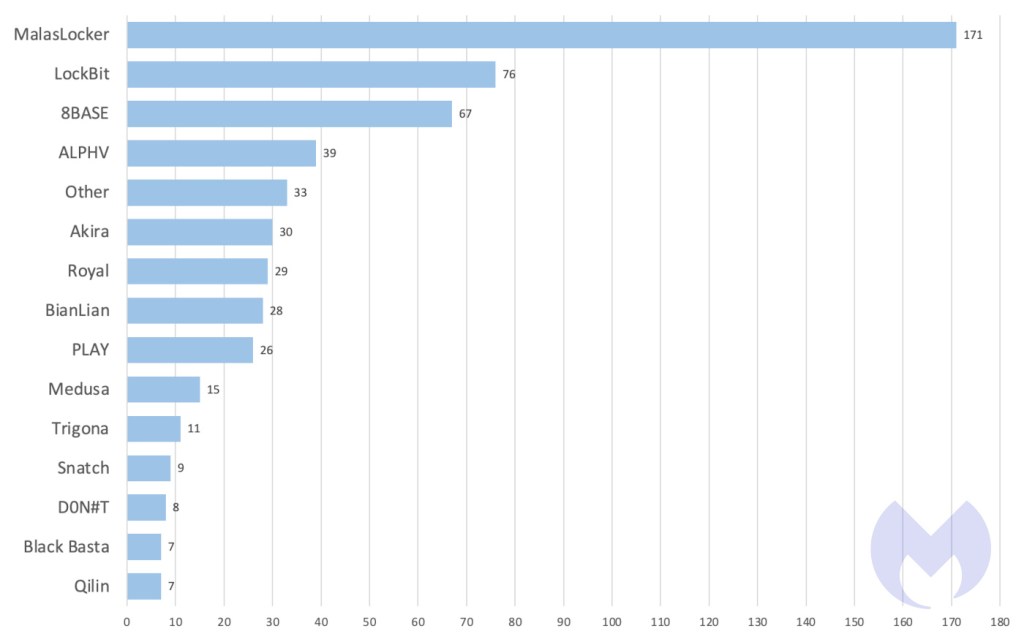
This isn’t the first time this year a gang has overhauled LockBit and climbed to the top spot on our monthly charts. In April Cl0p rose to the number one spot by compromising over 100 victims with a zero-day vulnerability in the widely-used managed file transfer software GoAnywhere MFT.
This month, MalasLocker’s meteoric rise to the top can be explained along similar lines.
MalasLocker attacked vulnerabilities in Zimbra servers, including CVE-2022-24682, to enable remote code execution (RCE). Zimbra Collaboration, formerly known as the Zimbra Collaboration Suite (ZCS) is a collaborative software suite that includes an email server and a web client.
What sets MalasLocker most apart, however, is its unique ‘charitable’ twist. Rather than demanding ransoms, it asked victims to donate to its approved charities.
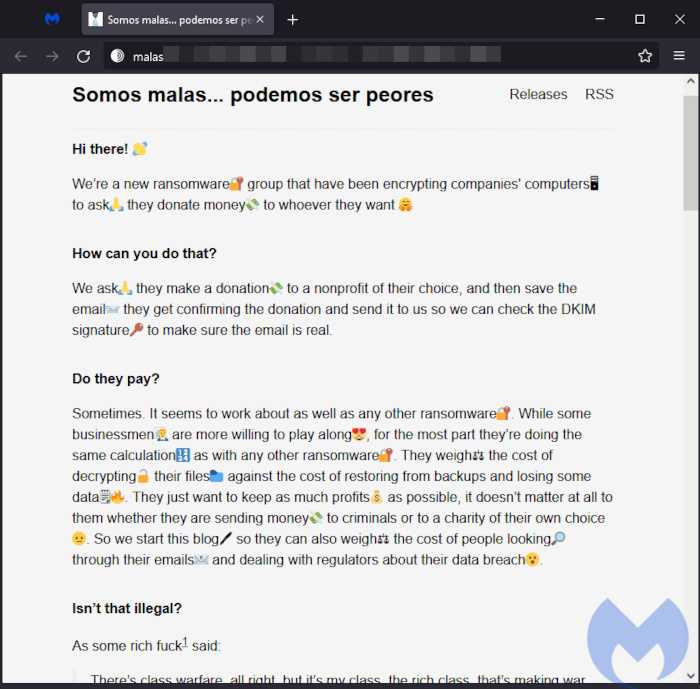
Needless to say, it is highly unusual for a ransomware gang to purport to attack organizations on altruistic grounds. We haven’t seen it once since keeping track of gangs in early 2022.
“Unlike traditional ransomware groups, we’re not asking you to send us money. We just dislike corporations and economic inequality,” reads the MalasLocker ransom note README.txt.
One might assume that a ransomware gang principally opposed to corporations and economic inequality might disproportionately target larger and more wealthy organizations, but this isn’t necessarily the case. The gang’s blog suggests it’s open to targeting businesses of all sizes, so long as they aren’t located in “Latin America, Africa, or other colonized countries.”
We are completely unmoved by MalasLocker’s supposed altruism. Ransomware gangs (and cybercriminals in general) have a long and storied history of writing long and tedious tracts justifying their criminal activity with grandiose claims.
MalasLocker is no different. We read its manifesto so you don’t have to, and the only line you need to pay any attention to is the one that reads “so we will become just another ransomware group.”
So far, we have no confirmation that MalasLocker is keeping its word for a decryptor when a victim donates money to a charity.
Italy and Russia emerge as targets
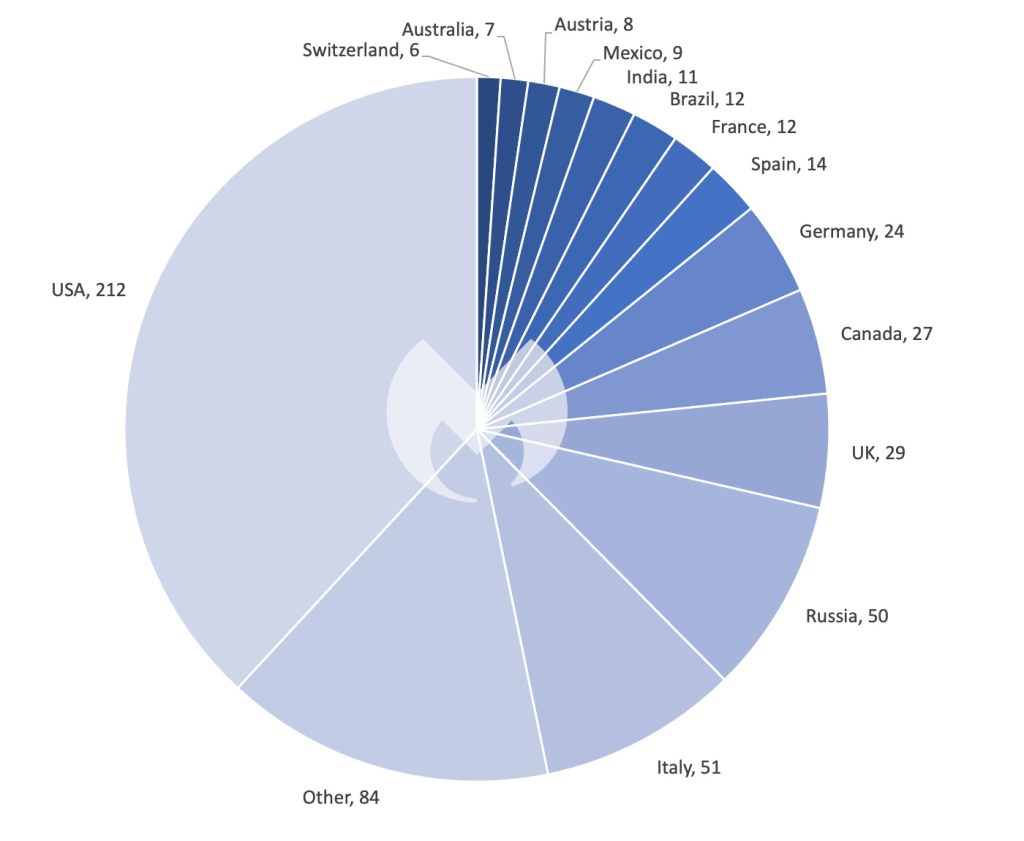
The upswing in ransomware activity in Italy and Russia in May is striking. Both countries were propelled into the top three most targeted nations in May, a list typically dominated by the USA and the UK.
Italy saw more than a six-fold increase from the month before, and Russia went from zero reported attacks to 50 in a single month. For comparison, Italy had only eight reported ransomware incidents in April, while Russia wasn’t even listed. Similarly, in March, Russia had no reported incidents, and Italy had just eight.
The surge in attacks on these two countries is entirely due to MalasLocker, which hit more targets in Russia and Italy than anywhere else. We assume that this is not a matter of deliberate targeting but simply a matter of where there were vulnerable targets.
Known MalasLocker attacks by country, May 2023
Traditionally, most ransomware gangs have avoided targeting Russia and the Commonwealth of Independent States (CIS) to prevent attracting the attention of local authorities who otherwise turn a blind eye to them.
Either MalasLocker isn’t based in the CIS and therefore doesn’t fear the Federal Security Service (FSB), or they are going to have a very short stay in the ransomware charts.
Increased ransomware attacks on Education
The increase in ransomware attacks on the education sector in May is particularly concerning. May saw 30 known attacks—the highest we’ve seen in a single month since we started keeping records in early 2022, and the continuation of a trend that has seen a sustained increase over the past twelve months.
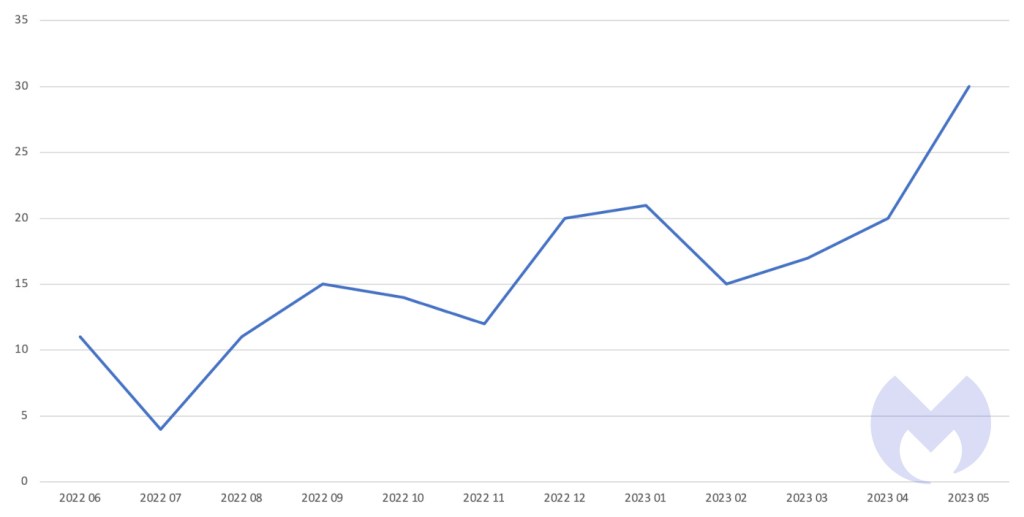
Known ransomware attacks against education, June 2022-May 2023
Between June 2022 and May 2023, Vice Society attacked more education targets than any other gang—a specialization that should alarm schools, colleges, and universities everywhere.
A new norm?
Ransomware gangs seem to be adopting a new modus operandi: Exploiting known vulnerabilities for multi-target attacks. This year we have seen Cl0p and MalasLocker attack multiple targets simultaneously with (presumably automated) targeting of specific system weaknesses, expanding the scale and impact of their ransomware operations.
Cl0p, for example, has a history of exploiting platforms like Accellion FTA and GoAnywhere MFT. In April, it shifted its focus to a vulnerability in another popular platform, PaperCut.
In June, as we prepared this report, it emerged that Cl0p was been exploiting yet another vulnerability, this time in the widely used file transfer software MOVEit Transfer. The gang started exploiting the vulnerability on May 27th, during the US Memorial Day holiday.
A security bulletin released on May 31, 2023 by Progress Software states:
“A SQL injection vulnerability has been found in the MOVEit Transfer web application that could allow an un-authenticated attacker to gain unauthorized access to MOVEit Transfer’s database. Depending on the database engine being used (MySQL, Microsoft SQL Server, or Azure SQL), an attacker may be able to infer information about the structure and contents of the database in addition to executing SQL statements that alter or delete database elements.“
This approach is unusual and should concern us all because it has the potential to make ransomware attacks more scalable.
New players
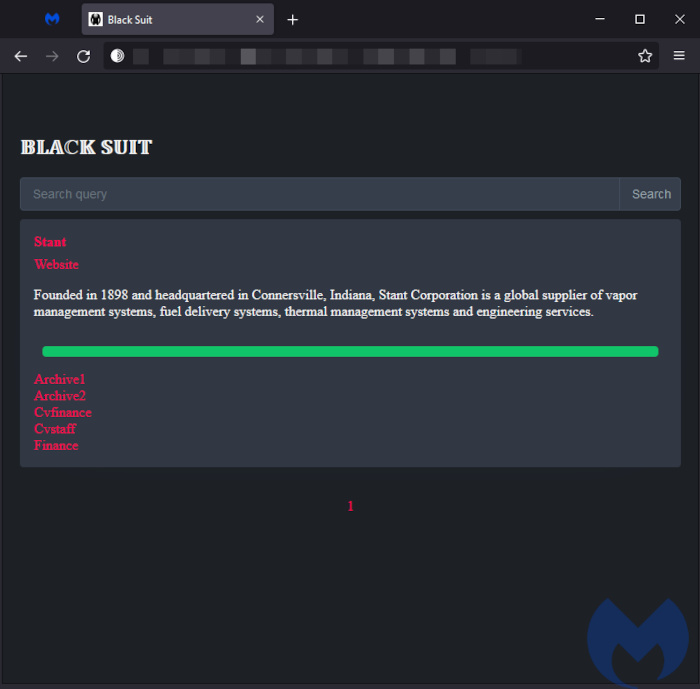
BlackSuit
BlackSuit is a new ransomware that is strikingly similar to Royal, sharing 98% of its code. Last month, BlackSuit targeted both Windows and Linux hosts.
BalckSuit could be a new variant developed by Royal’s authors, a mimicry attempt using similar code, an affiliate of the Royal ransomware gang running its own modifications, or even a breakaway group from the Royal ransomware gang.
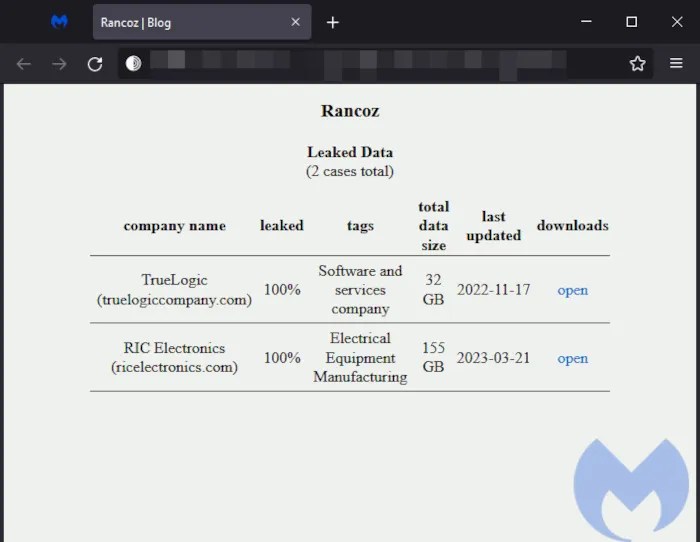
Rancoz
Rancoz is a new ransomware variant which shares similarities with Vice Society. Its sophistication lies in its ability to modify existing code from leaked source codes to target specific industries, organizations, or geographic regions, increasing its attack efficacy and ability to evade detection.
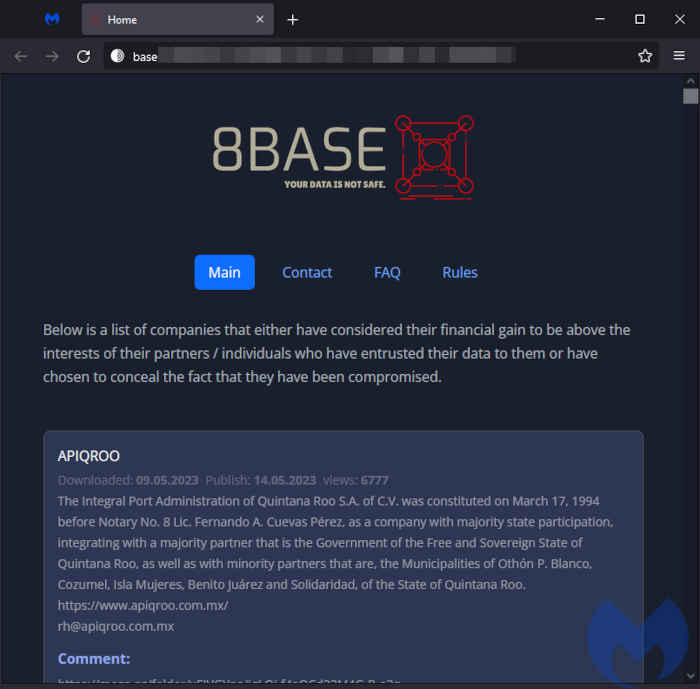
8BASE
8Base is a newly discovered ransomware gang which, despite only recently gaining attention, has been in operation since April 2022. In May, it had a total of 67 victims.
Predominantly targeting small and medium-sized businesses (SMBs), 8Base has attacked mainly companies within the Professional/Scientific/Technical sector, comprising 36% of known attacks, followed by Manufacturing at 17%. Geographical analysis of the victims suggests a concentration in America and Europe, with the United States and Brazil being the most targeted countries.
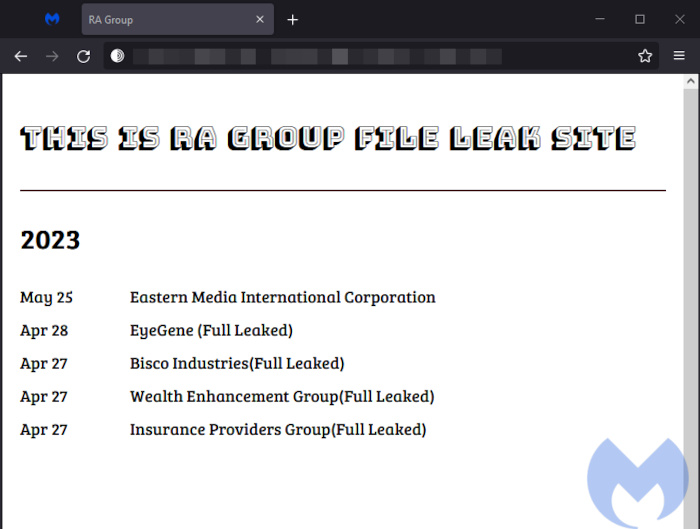
RA Group
RA Group is a new ransomware primarily focusing its attacks on pharmaceutical, insurance, wealth management, and manufacturing firms located in the United States and South Korea.
The RA Group employs an encryptor derived from the leaked source code of Babuk ransomware, an operation that ceased in 2021. The encryptor employs intermittent encryption, which alternates between encrypting and not encrypting sections of a file to expedite the encryption process, but leaves some data partially recoverable.
How to avoid ransomware
- Block common forms of entry. Create a plan for patching vulnerabilities in internet-facing systems quickly; disable or harden remote access like RDP and VPNs; use endpoint security software that can detect exploits and malware used to deliver ransomware.
- Detect intrusions. Make it harder for intruders to operate inside your organization by segmenting networks and assigning access rights prudently. Use EDR or MDR to detect unusual activity before an attack occurs.
- Stop malicious encryption. Deploy Endpoint Detection and Response software like ThreatDown EDR that uses multiple different detection techniques to identify ransomware, and ransomware rollback to restore damaged system files.
- Create offsite, offline backups. Keep backups offsite and offline, beyond the reach of attackers. Test them regularly to make sure you can restore essential business functions swiftly.
- Don’t get attacked twice. Once you’ve isolated the outbreak and stopped the first attack, you must remove every trace of the attackers, their malware, their tools, and their methods of entry, to avoid being attacked again.
ThreatDown EDR and MDR removes all remnants of ransomware and prevents you from getting reinfected. Want to learn more about how we can help protect your business? Get a free trial below.
Cybercrime Has Gone Machine-Scale
AI is automating malware faster than security can adapt.
Get the facts Read the 2026 State of MalwareCybercrime Has Gone Machine-Scale
AI is automating malware faster than security can adapt.
Get the facts Read the 2026 State of Malware


