Ransomware review: October 2023
Threat Intelligence Team
Threat Intelligence Team
This article is based on research by Marcelo Rivero, Malwarebytes’ ransomware specialist, who monitors information published by ransomware gangs on their Dark Web sites. In this report, “known attacks” are those where the victim did not pay a ransom. This provides the best overall picture of ransomware activity, but the true number of attacks is far higher.
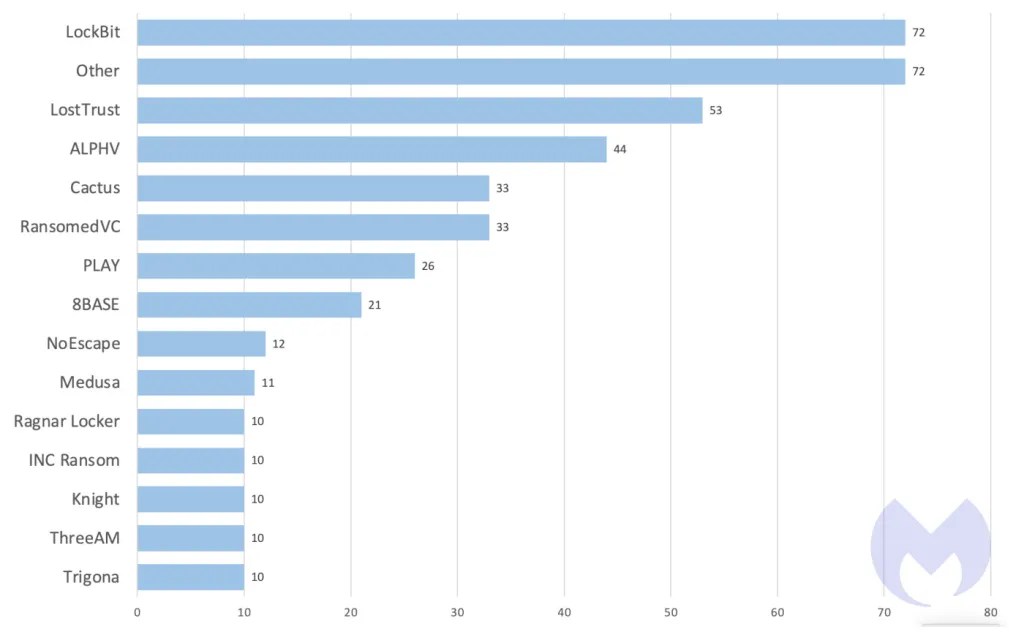
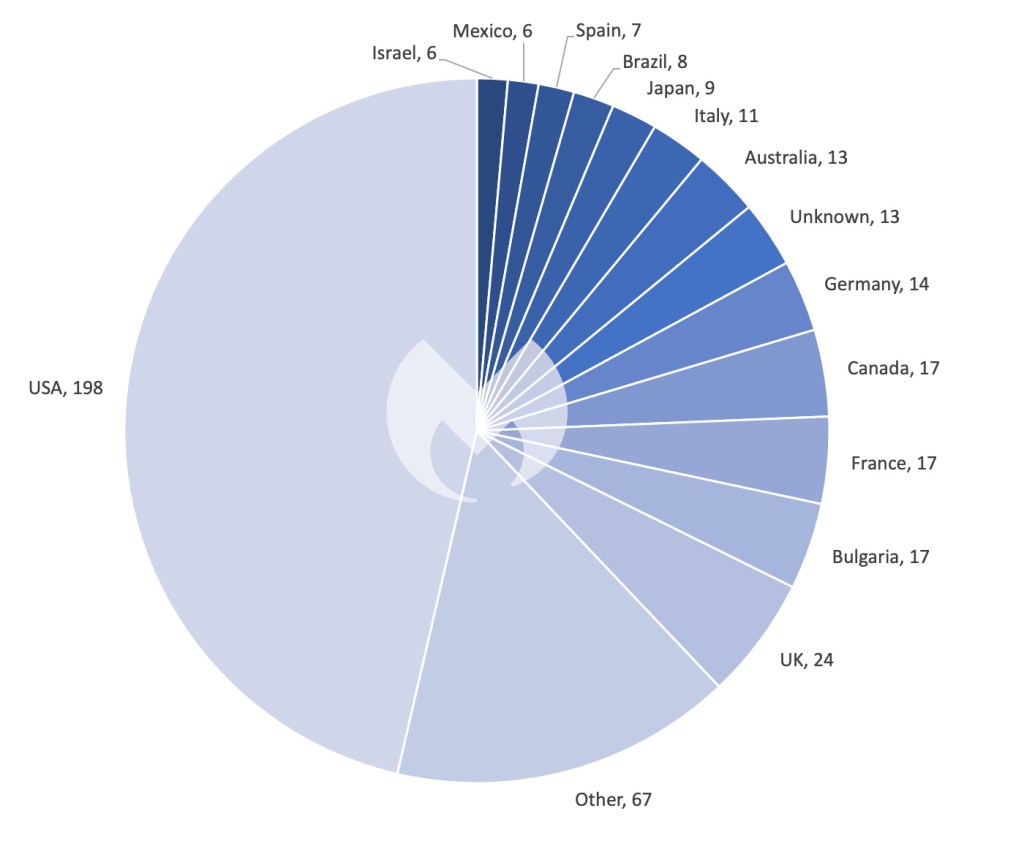
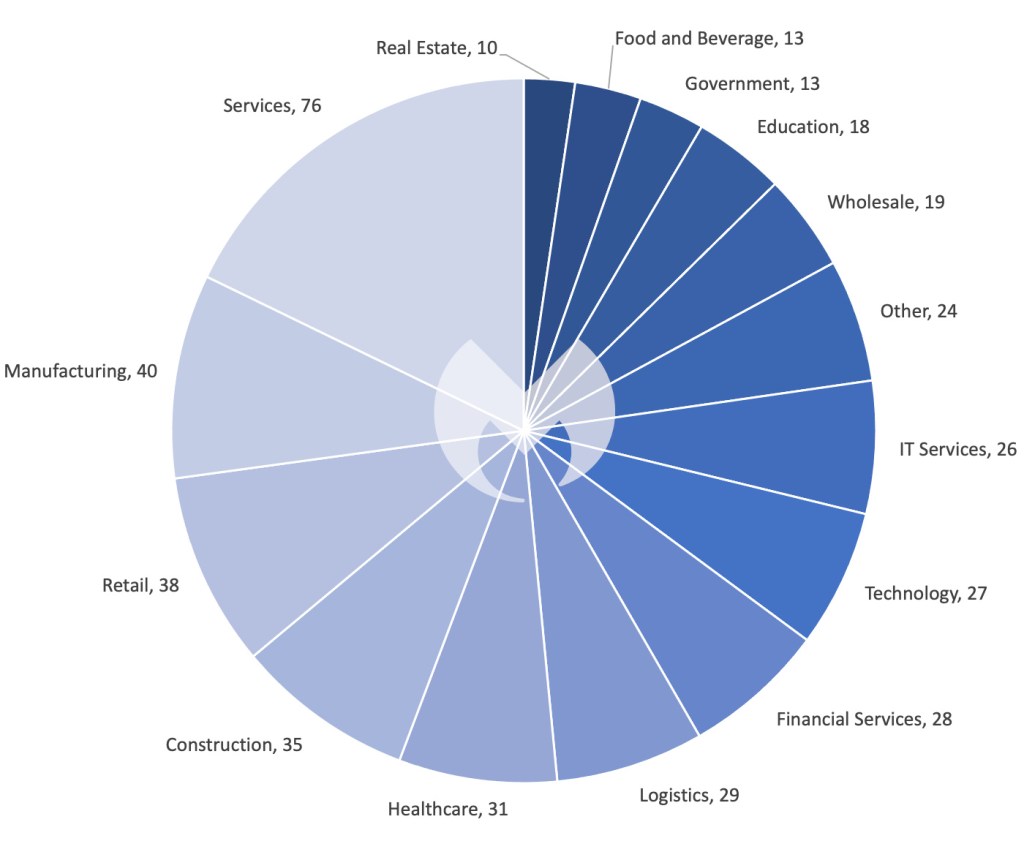
In September, we recorded a total of 427 ransomware victims. As usual, Lockbit (72) led the charts. New players we observed included LostTrust (53), ThreeAM (10), and CiphBit (8).
Last month, MGM Resorts and Caesar Entertainment made headlines after being attacked by an ALPHV affiliate known as Scattered Spider. Other significant attacks included Sony, targeted by RansomedVC, and Johnson Controls, targeted by Dark Angels.
The attacks on MGM Resorts and Caesar Entertainment—which collectively own most of the casino-hotel properties on the Vegas Strip—resulted in the former losing $100 million in earnings and the latter making a reported $15 million ransom payment to the attackers. In both cases, significant amounts of customer data were stolen.
In other news, both LockBit and the Akira ransomware gang, the latter of which has tallied 125 victims since we first began tracking them in April 2023, were confirmed last month to be exploiting a specific zero-day flaw (CVE-2023-20269) in Cisco VPN appliances. On a related note, the effect of CL0P’s MOVEit zero-day campaign was further revealed last month when the National Student Clearinghouse and BORN Ontario Child Registry disclosed data breaches attributed to the group.
Last month’s two high-profile casino breaches were an interesting case study in the nuances of the RaaS affiliate landscape, the asymmetric dangers of phishing, and of two starkly different approaches to ransomware negotiation.
Primarily hailing from the US and the UK, and founded in May 2022, Scattered Spider launched two casino attacks that have given the group attention on a scale rarely seen with RaaS affiliates—whose attacks are normally grouped under whichever RaaS gang supplied them with the ransomware (in this case, ALPHV).
One possible explanation for Scattered Spider’s unusual spotlight resides in the group’s level of sophistication. RaaS, by its very nature, has a low barrier to entry, meaning many affiliates are relatively unsophisticated or possess only moderate technical skills. Scattered Spider, on the contrary, highlights the peril posed when ready-made RaaS software merges with seasoned experience: In both of their casino breaches, the group employed advanced tactics, techniques, and procedures (TTPs), including in-depth reconnaissance, social engineering, and advanced lateral movement techniques.
Scattered Spider typically kick off their attacks by manipulating employees into granting access, and their breaches of MGM Resorts and Caesar Entertainment began no differently. For the MGM breach, Scattered Spider used LinkedIn to pinpoint an MGM Resorts employee, subsequently impersonating them and contacting the company’s help desk requesting account access. Alarmingly, this ploy unveiled a gaping security flaw at MGM—the absence of a stringent user verification protocol at the service desk. After gaining an initial foothold, they escalated their access to administrative rights and subsequently launched a ransomware attack.
Or, as vx-underground so poetically put it: “A company valued at $33,900,000,000 was defeated by a 10-minute conversation.”
Less specifics are known about the exact social engineering scheme used in the Caesar Entertainment breach, but judging by the company’s SEC filing, it’s safe to say Scattered Spider used a similar help desk style scam. Both breaches remind us that, whether ransomware is deployed or not, the human element remains one of the most vulnerable spots in an organization’s defenses.
Additionally, the aftermath of these attacks highlights the absence of a one-size-fits-all solution when it comes to paying attackers ransom. According to the Wall Street Journal, MGM Resorts refused to pay the attackers while Caesars Entertainment, in an effort to prevent their stolen data from being leaked, reportedly paid attackers a ransom worth approximately $15 million. It’s worth reiterating, of course, that despite whatever internal calculus Caesars Entertainment made when deciding to pay the ransom, there is no guarantee that attackers will hold up their end of the bargain. The company’s public willingness to pay also makes them a vulnerable target for further attacks.
On the other hand, there’s no denying that a data leak, especially of sensitive customer or corporate information, can cause a level of reputational harm that some companies might view as impossible to risk taking on—even if it means paying a substantial amount to thieves who may or may not honor their word.
New Players
LostTrust
LostTrust is a likely rebrand from the MetaEncryptor ransomware gang we first spotted in August 2023. In September, they had a staggering 53 victims. The reason for the rebrand is unclear at present.
ThreeAM (3AM)
ThreeAM, a new ransomware family used as a fallback in failed LockBit attack, had 10 victims in September.
CiphBit
While CiphBit has been posting victims on their dark website since April, the group wasn’t discovered in-the-wild until last month. In September, they reported two new victims, bringing their total to eight victims to-date.
How to avoid ransomware
- Block common forms of entry. Create a plan for patching vulnerabilities in internet-facing systems quickly; disable or harden remote access like RDP and VPNs; use endpoint security software that can detect exploits and malware used to deliver ransomware.
- Detect intrusions. Make it harder for intruders to operate inside your organization by segmenting networks and assigning access rights prudently. Use EDR or MDR to detect unusual activity before an attack occurs.
- Stop malicious encryption. Deploy Endpoint Detection and Response software like ThreatDown EDR that uses multiple different detection techniques to identify ransomware, and ransomware rollback to restore damaged system files.
- Create offsite, offline backups. Keep backups offsite and offline, beyond the reach of attackers. Test them regularly to make sure you can restore essential business functions swiftly.
- Don’t get attacked twice. Once you’ve isolated the outbreak and stopped the first attack, you must remove every trace of the attackers, their malware, their tools, and their methods of entry, to avoid being attacked again.
Cybercrime Has Gone Machine-Scale
AI is automating malware faster than security can adapt.
Get the facts Read the 2026 State of MalwareCybercrime Has Gone Machine-Scale
AI is automating malware faster than security can adapt.
Get the facts Read the 2026 State of Malware


