
Threat actors ride the hype for newly released Arc browser
Google Chrome has been the dominant web browser for years now, which is why it may come as a surprise to hear of a startup, not even based in Silicon Valley, called The Browser Company offering a new take on the “window to the internet”.
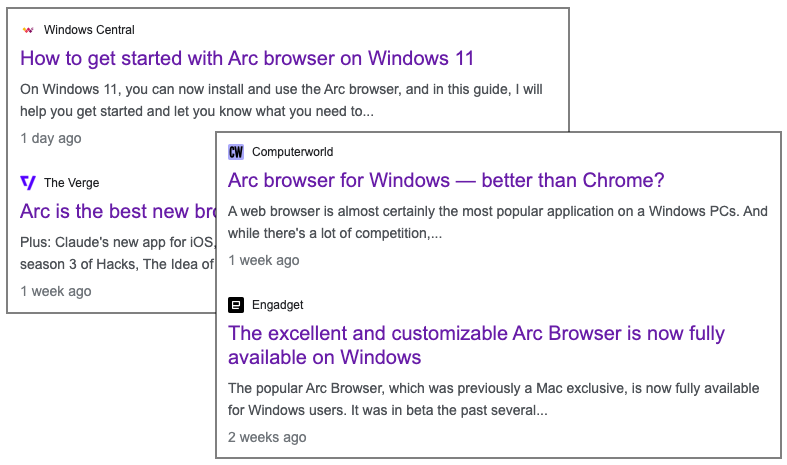
The Arc browser has been available for MacOS since July 2023, but the Windows version was only released a couple of weeks ago. What’s unique is the hype around Arc, but also the glowing reviews it has earned in a relatively short time span.
The excitement about Arc was not lost on cyber criminals who are fully aware people will be interested in trying out the new browser. We saw a new malvertising campaign using Google search ads for Arc, which is exactly where potential victims will come from.
In this blog post, we review this latest scheme and provide details on the malware that’s being installed. We noted a clever use of the MEGA cloud platform to act as a command and control server, coupled with other tricks such as embedding code inside image files. We have already reported the malicious ads to Google.
Arc browser earns industry accolades
The Browser Company made a big splash with its new take on the browser. There is no doubt that the hype plays a big factor in user adoption, but reviews from top publications are also a big driving force. While the Mac version of Arc browser was already available, the Windows release was announced just a couple of weeks ago.
Threat actor immediately impersonates Arc brand
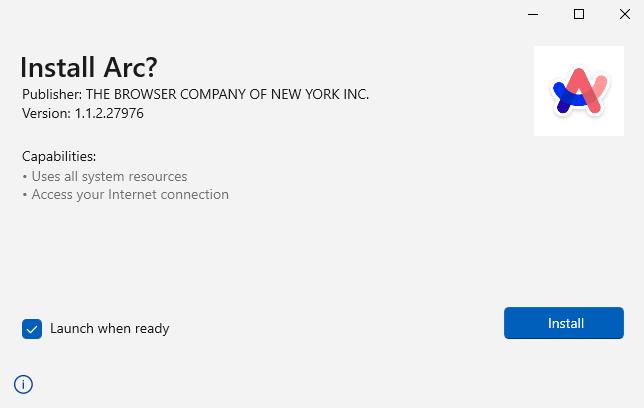
We observed an ad campaign impersonating the Arc browser that looks entirely legitimate with official logo and website. A search for “arc installer” or “arc browser windows” resulted in the following two ads being shown:
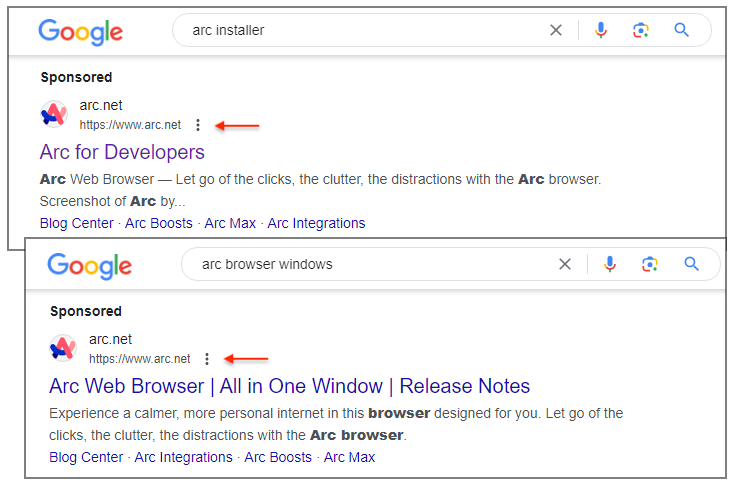
Using Google’s Ad Transparency Center, we connected them to the following advertiser from Ukraine:
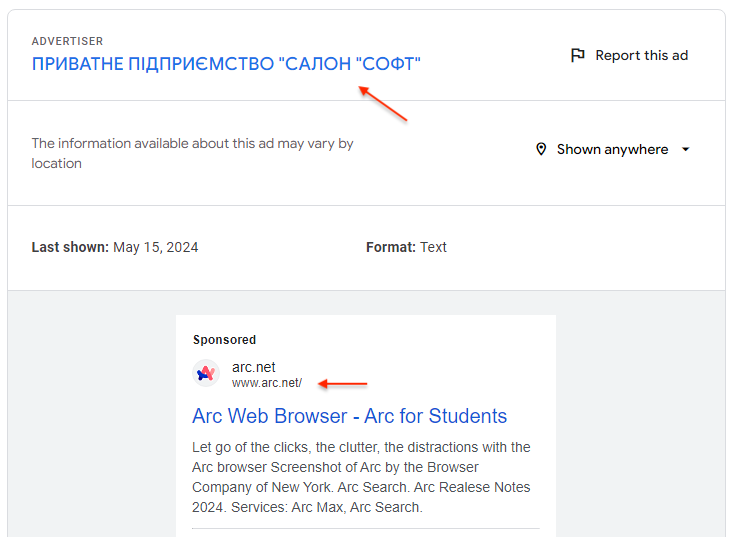
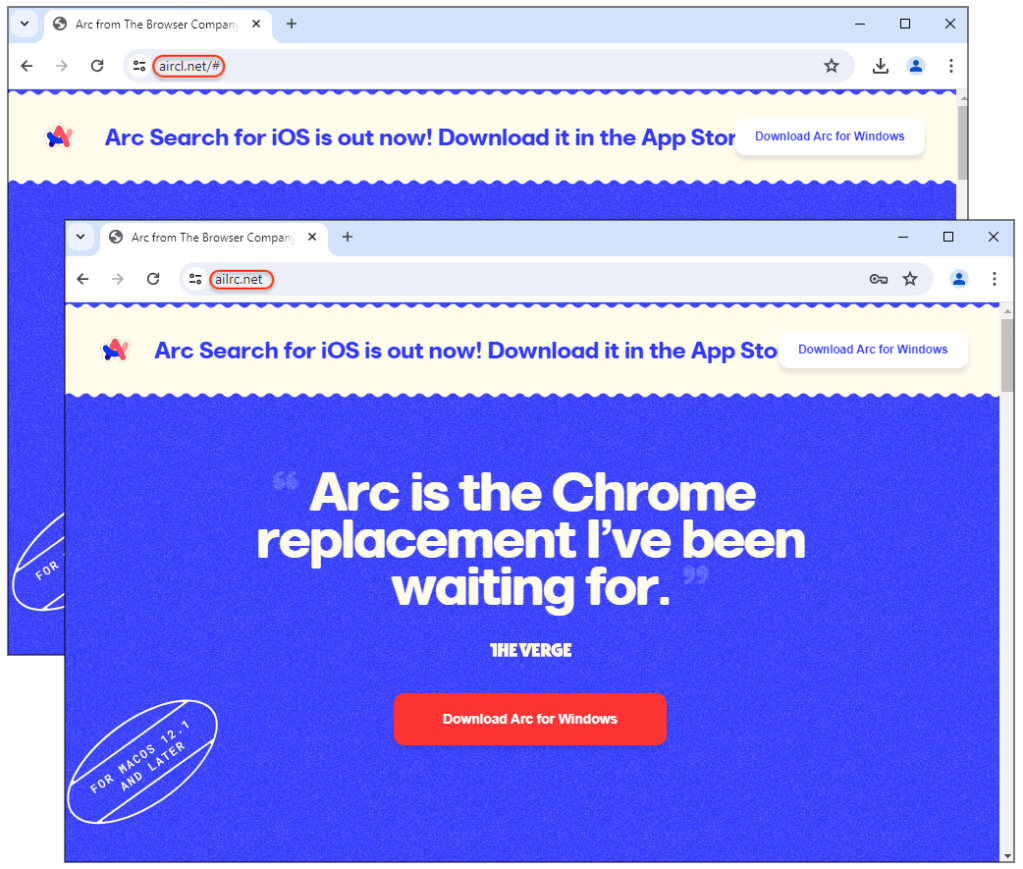
The threat actor already registered domain names that victims will be redirected to. The template even includes some of the news headlines celebrating the Windows release:
Malware payload
When you download “Arc for Windows” from these websites, you are actually downloading malware. In this case, the threat actor used a unique way of packaging their malware that we had not seen before.
The main installer (ArcBrowser.exe) is an executable that itself contains two other executables. As part of the decoy, one of them will retrieve a Windows installer for the legitimate Arc software.
In the background, Arc.exe contacts the cloud platform MEGA via its developer’s API. We believe the threat actor is using MEGA as a command and control server to send and receive data. The first query authenticates the threat actor (they are using a disposable email address from yopmail):
https://g[.]api[.]mega[.]co[.]nz/cs?id=[]
[{"a":"us0","user":"vivaldi.dav@yopmail[.]com"}]
It is followed by a series of queries and responses that are encoded, presumably with the user data.

Next is a request to a remote site to download the next stage payload:
theflyingpeckerheads[.]com/bootstrap.exe
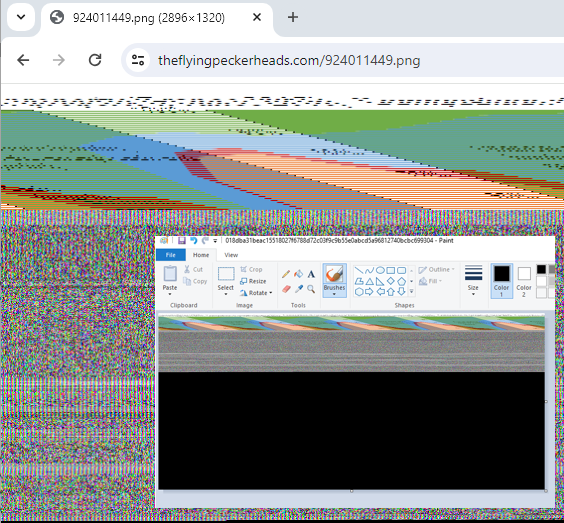
Once that payload is executed, it retrieves a fake PNG image that hides malicious code:
theflyingpeckerheads[.]com/924011449.png
We get yet another payload, dropped to disk as JRWeb.exe.
While working on this sample, we saw another version of the boostrap.exe file which did not retrieve a PNG file. This file was downloaded from the same location, with the same name but had a different size.
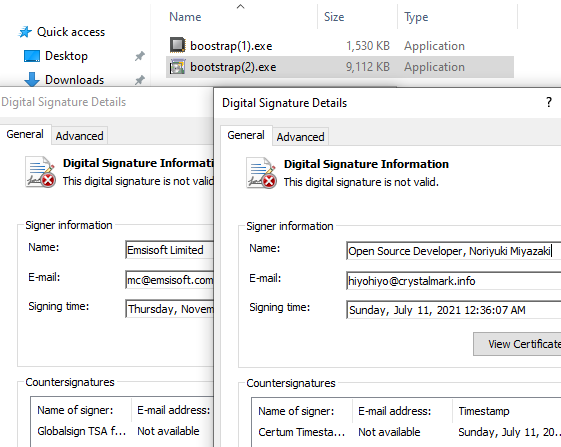
That second version uses a legitimate Python executable to inject code into MSBuild.exe, just like the previous one.
C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe
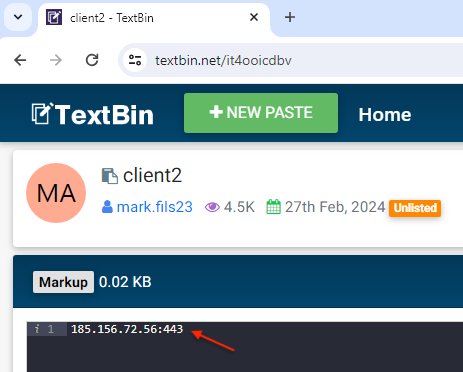
At that point, the malware will query a paste site to retrieve a malicious IP address (presumably another command and control server):
https://textbin[.]net/raw/it4ooicdbv
The paste was first created in February and has 4.5K views:
Based on similar previous attacks, the payload is likely dropping an information stealer. ThreatDown’s customers were already protected thanks to the detection of the malicious bootstrap.exe process.

Conclusion
Some of the best social engineering attacks happen when users are lured with well known brands. We have seen countless cases of brand impersonations via malicious ads targeting different types of victims. But online criminals will also leverage newer brands that are trending, and Arc is the perfect example of a new piece of software that many people will be looking to try out.
It is more important than ever to be extremely cautious when it comes to sponsored results. Often times, there is no easy way to determine whether an ad is legitimate or not. Criminals are able to create malicious installers that can evade detection and lead to compromise via a series of steps. Fortunately, this is also where Endpoint Detection and Response (EDR) can be helpful, as a set of events can be tied to an actual attack.
Indicators of Compromise
Decoy sites
ailrc[.]net
aircl[.]net
Malicious Arc installer
ArcBrowser.exe
3e22ed74158db153b5590bfa661b835adb89f28a8f3a814d577958b9225e5ec1
Arc.exe loads the Windows installer for the legitimate Arc Browser via
revomedia[.]com/Arc.appinstaller
Followup payload
theflyingpeckerheads[.]com/bootstrap.exe
b8ae9aa480f958312b87877d5d44a9c8eac6a6d06a61ef7c51d4474d39357edb
34f4d749af50678a0bda6f38b0c437de3914a005f0d689aa89769c8c9cb8b264
Bootstrap.exe downloads PNG from
theflyingpeckerheads[.]com/924011449.png
018dba31beac15518027f6788d72c03f9c9b55e0abcd5a96812740bcbc699304
Final payload
JRWeb.exe
6c30c8a2e827f48fcfc934dd34fb2cb10acb8747fd11faae085d8ad352c01fbf
C2
185.156.72[.]56
Cybercrime Has Gone Machine-Scale
AI is automating malware faster than security can adapt.
Get the facts Read the 2026 State of MalwareCybercrime Has Gone Machine-Scale
AI is automating malware faster than security can adapt.
Get the facts Read the 2026 State of Malware


