A first look at the builder for LockBit 3.0 Black
A few months after the LockBit gang released version 3.0 of its ransomware, LockBit 3.0 Black, the builder for it has been leaked by what seems to be a disgruntled developer. LockBit has been by far the most widely used ransomware in 2022 and the appearance of the builder could make things worse. It is likely to be popular, so we could see new gangs appear that aren’t affiliated with the LockBit group but use its software, for example. We also expect to see fake packages offered online that infect the person running the builder, rather than building ransomware for them.
The builder turned up in two different places and was leaked using two different online identities. But where it came from and why isn’t really that interesting, certainly not for people looking to defend against it. For that, what it can do and what the implications are, are far more interesting.
Testing
Malwarebytes ransomware researchers managed to get their hands on a copy of the builder and found that, sadly, building your own ransomware has never been easier.
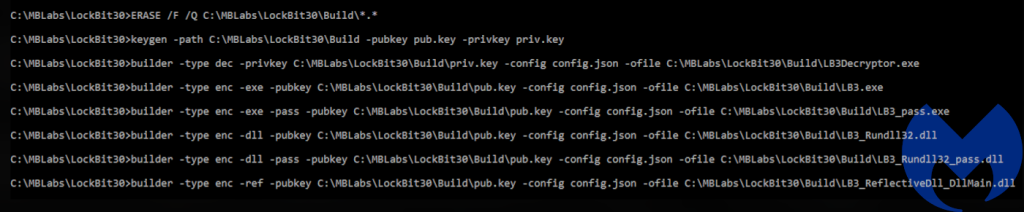
The whole builder actually only holds four files: An encryption key generator, keygen.exe, the actual
builder.exe, a modifiable configuration file, config.json, and a batch file to build all of the files called
build.bat.
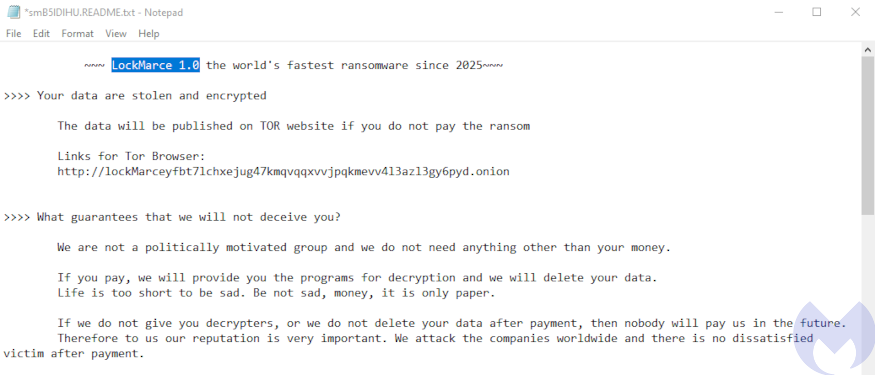
The builder offers a high level of customization. In the included example of the configuration file the ransomware operator can choose their own C2 server, choose the processes they want to terminate, modify the ransom note, and so on.
Once the operator has set the configuration they can start a batch file that produces all of the files they need to start a new ransomware campaign.
A blessing in disguise is that thie Lockbit 3.0 Black fixes a decryption bug that was present in previous versions. The new version encrypts and decrypts flawlessly. You absolutely don’t want to be infected with ransomware, but if you are, you want the process to be reliably reversible.
Mitigation
We recommend reading an expert view on simplifying the fight against ransomware, but to sum it up in a few bullet points:
- Stop initial access by turning off or hardening RDP, having a plan for how and when you’ll do your security updates, and training users to spot malicious emails.
- Make privilege escalation and lateral movement as hard as possible by using the principle of least privilege, segmenting your network, and deploying EDR.
- Use an anti-malware solution that can identify ransomware and can roll back infections.
- Keep your data safe with offsite, offline backups that are out of the reach of attackers.
- Accept that even with the best defences, breaches can still happen. Prepare a distaster recovery plan.
Cybercrime Has Gone Machine-Scale
AI is automating malware faster than security can adapt.
Get the facts Read the 2026 State of MalwareCybercrime Has Gone Machine-Scale
AI is automating malware faster than security can adapt.
Get the facts Read the 2026 State of Malware

