
FBI has 7,000 LockBit decryption keys available
During the Boston Conference on Cybersecurity, Federal Bureau of Investigation (FBI) Cyber Division Assistant Director Bryan Vorndran urged victims of the LockBit ransomware gang to contact the bureau’s Internet Crime Complaint Center (IC3).
LockBit sells ransomware-as-a-service (RaaS) to affiliates, criminal gangs who use the service to carry out ransomware attacks that encrypt a victim’s data. The victims are then instructed to pay a ransom for a unique decryption key that can undo the damage.
Vorndran explained that the FBI has over 7,000 LockBit decryption keys in its possession, meaning that it can help victims to recover data encrypted by the gang in past attacks. LockBit ransomware has impacted over 1,800 US victims, according to FBI stats.
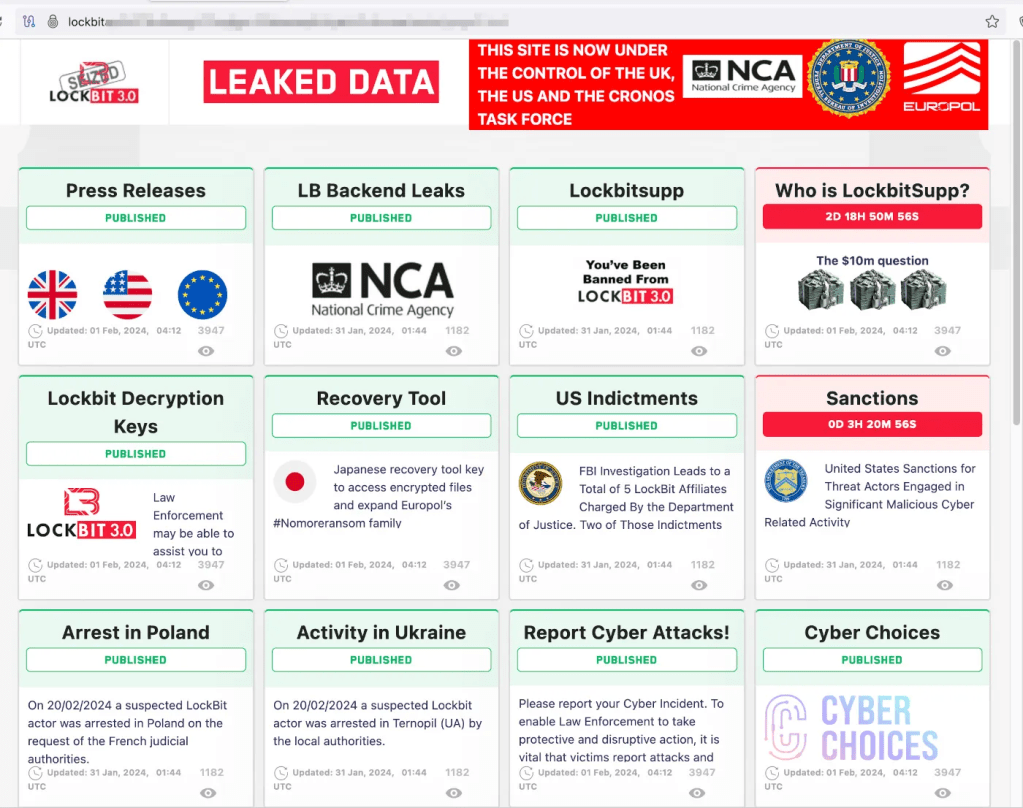
The decryption keys are a result of Operation Cronos, a multi-nation, multi-agency law enforcement action that caused serious disruption to the LockBit gang in February 2024. At the time, law enforcement said it had taken over LockBit’s administration environment, seized the infrastructure used by its data exfiltration tool, captured over 1,000 decryption keys, and frozen 200 cryptocurrency accounts. The UK’s National Crime Agency (NCA) also took over the LockBit dark web site and used it to troll the gang with a series of eye-catching announcements.
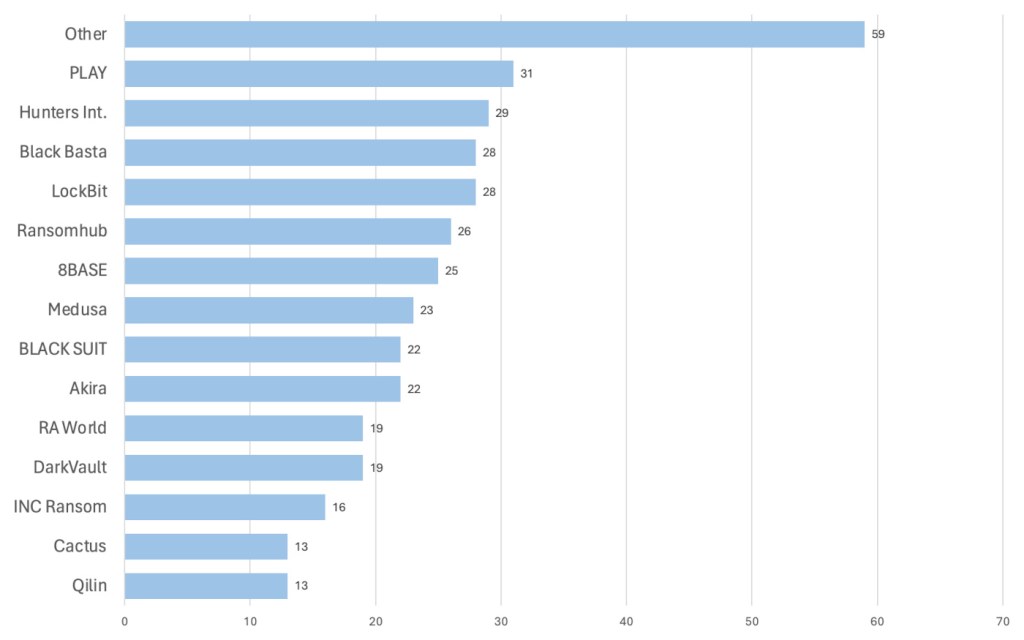
In ThreatDown’s May ransomware review, we noted that the group still hasn’t recovered from Cronos, and other gangs are now competing to be the dominant ransomware group, a spot that LockBit dominated for two years.
However, LockBit hasn’t disappeared, and is still active with new infrastructure. Its recent victims include Canadian pharmacy chain London Drugs.
The FBI ask victims to contact the IC3 by filling out the LockBit Victim Reporting Form.
How to avoid ransomware
- Block common forms of entry. Create a plan for patching vulnerabilities in internet-facing systems quickly; and disable or harden remote access like RDP and VPNs.
- Prevent intrusions. Stop threats early before they can even infiltrate or infect your endpoints. Use endpoint security software that can prevent exploits and malware used to deliver ransomware.
- Detect intrusions. Make it harder for intruders to operate inside your organization by segmenting networks and assigning access rights prudently. Use EDR or MDR to detect unusual activity before an attack occurs.
- Stop malicious encryption. Deploy Endpoint Detection and Response software like ThreatDown EDR that uses multiple different detection techniques to identify ransomware, and ransomware rollback to restore damaged system files.
- Create offsite, offline backups. Keep backups offsite and offline, beyond the reach of attackers. Test them regularly to make sure you can restore essential business functions swiftly.
- Don’t get attacked twice. Once you’ve isolated the outbreak and stopped the first attack, you must remove every trace of the attackers, their malware, their tools, and their methods of entry, to avoid being attacked again.
Cybercrime Has Gone Machine-Scale
AI is automating malware faster than security can adapt.
Get the facts Read the 2026 State of MalwareCybercrime Has Gone Machine-Scale
AI is automating malware faster than security can adapt.
Get the facts Read the 2026 State of Malware


