GachiLoader adopts AI skill lure
AI skills are threat actors’ newest and most dangerous lures.
In our previous post, Weaponizing autonomy: The rise of malicious AI agent skills, we described how threat actors are beginning to use the AI agent skill format as an attack vector—skills that execute malicious code under the cover of a trusted, legitimate application. At the time, we focused on skills that embedded malicious instructions directly.
The sample analyzed here represents the next step in that evolution. The skill itself contains no malicious code at all. Instead, it is a pure social engineering vehicle: A convincingly packaged OpenClaw skill whose only purpose is to trick the user into downloading and running a Windows binary. That binary turns out to be the latest iteration of GachiLoader, delivering Rhadamanthys infostealer via fileless injection, with a Polygon blockchain smart contract as its C2 resolver.
The attack chain has two distinct tracks: A graphical Electron installer, and Node.js Single Executable Applications (SEA), but both converge on the same payload.
The GitHub infrastructure: Built for OpenClaw victims
The payload delivery infrastructure is hosted on the GitHub account blueberywoodsym, a throwaway account with no contribution history, created exclusively for this campaign. What is notable is that the entire releases page is dressed up around the OpenClaw brand, with three successive releases named to match the stages a victim would expect to encounter during a legitimate skill installation.
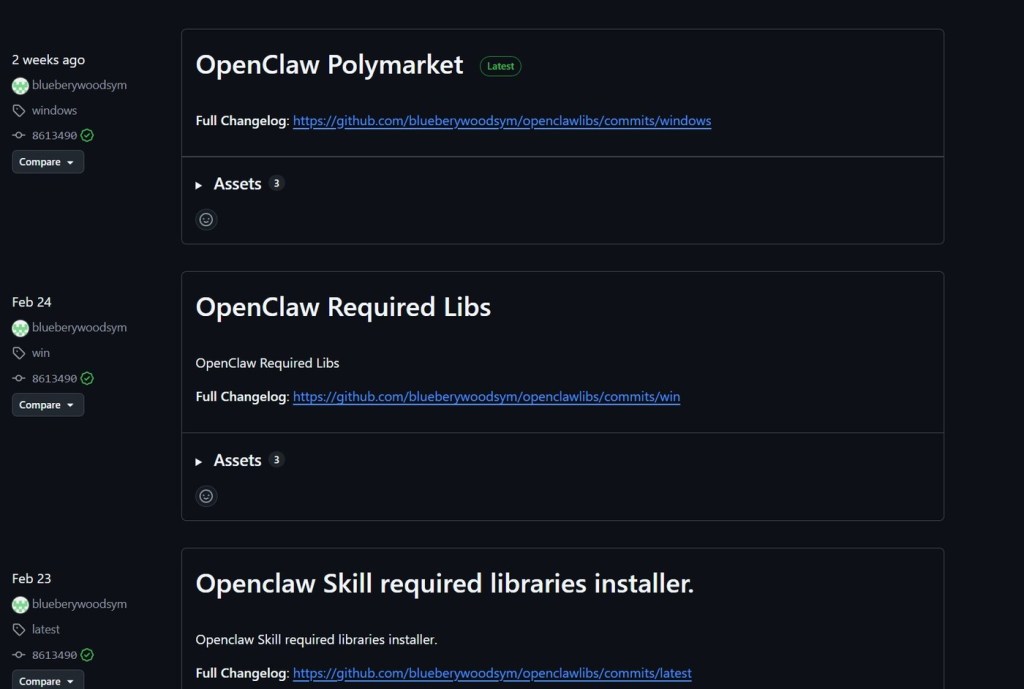
The three releases represent two distinct delivery mechanisms:
- OpenClaw Skill required libraries installer and OpenClaw Required Libs (Feb 23–24) — Node.js Single Executable Applications.
- OpenClaw Polymarket (latest) — an Electron application.
Both tracks deliver the same final payload: GachiLoader → Rhadamanthys.
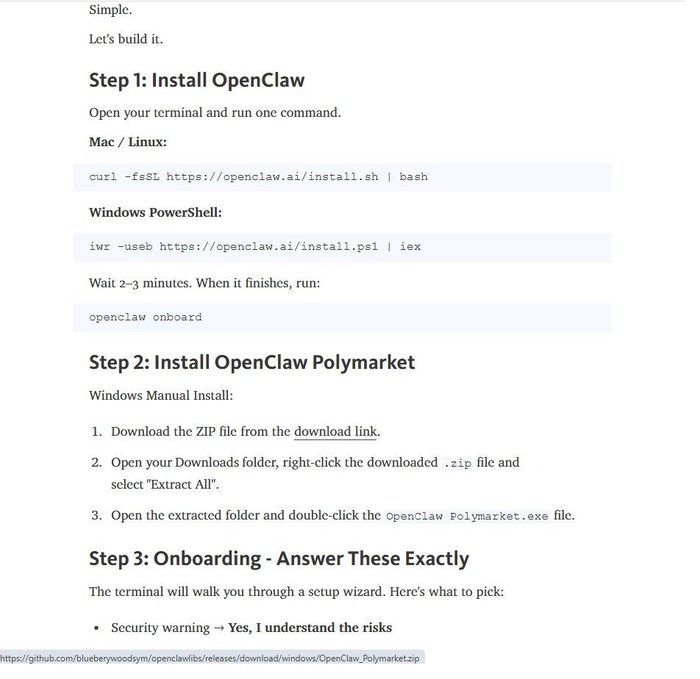
A README is all it takes
The attack begins before any binary is run. The skill package’s READ ME BEFORE INSTALL.htm is a locally saved copy of a Telegraph blog post titled “How Building a Weather Polymarket Bot with OpenClaw Skill and turn 100$ → 8000$”. It constructs a plausible arbitrage narrative: NOAA weather forecasts are accurate, Polymarket’s temperature-based betting markets have incorrect pricing, and an automated bot can exploit this gap for profit. To make the story more convincing, it references real services.
Step 2 of the file directs victims to download a zipped Polymarket.exe and run OpenClaw Polymarket.exe from the throwaway GitHub account.
Track 1: The Node.js SEA binaries
The two earlier releases are Node.js Single Executable Applications, self-contained binaries that bundle a Node.js runtime with an obfuscated JavaScript payload. Under analysis, they follow the GachiLoader execution pattern precisely: They drop a .node file in TEMP that acts as a loader for the Rhadamanthys stealer.
The C2 address is not hardcoded. Instead, it queries a Polygon smart contract to retrieve the C2 *.onfinality.pro. This is the defining characteristic of GachiLoader: The C2 lives immutably on-chain.
The injected PE is Rhadamanthys. Active modules in the sample analyzed: browsers, crypto wallets, Telegram, Outlook, VPN clients, FTP clients, password managers, screenshots, and hardware ID.
Track 2: The Electron dropper
The most recent release uses a NullSoft Installer application that drops and executes the Electron bundle in a randomly named folder under %TEMP%.
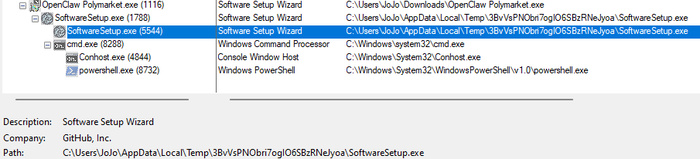
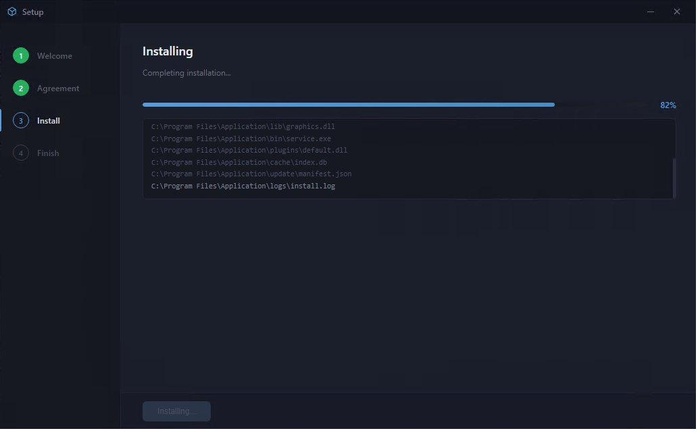
The Electron application starts with the launch of SoftwareSetup.exe, presenting itself as a convincing four-step installation wizard complete with a progress bar and a scrolling log of file paths. All of it is fabricated; no files are written to disk during this phase. The UI exists solely to keep the victim occupied and reinforce the impression of a legitimate installation.
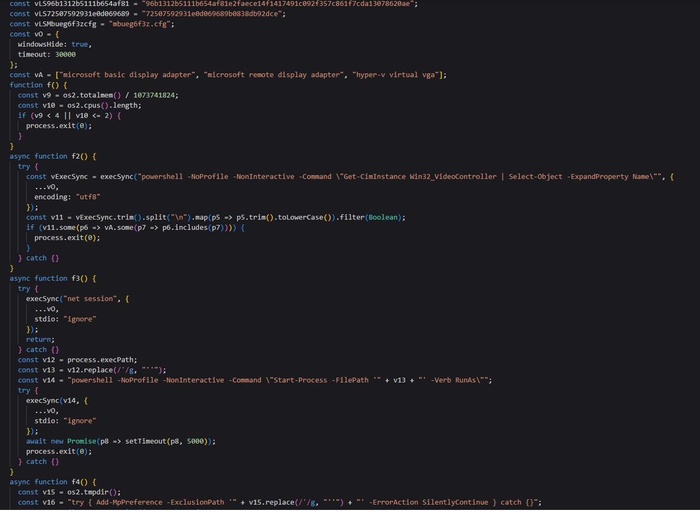
When the user clicks Install, the renderer process sends an IPC message to the Electron main process, where all the actual malicious logic resides. Before executing the payload, the main process performs a series of evasion checks:
- Anti-VM detection via GPU enumeration using Win32_VideoController.
- Sandbox detection by verifying that the system has more than 2 CPU cores and at least 4GB of RAM.
- Privilege escalation via Start-Process -Verb RunAs, forcing a UAC prompt to obtain administrator rights.
Once the checks pass, the main process kills SecHealthUI.exe and adds the %TEMP% directory to Windows Defender’s exclusion list before proceeding with payload execution.
The bundled file mbueg6f3z.cfg, an AES-256-CBC encrypted PE, is then decrypted using a hardcoded key and IV embedded in the main process. The resulting binary is written to %TEMP% as a randomly named .node file and launched as fully detached via spawn().
The dropped binary is Themida-packed, consistent with the packing scheme observed in previous GachiLoader payload variants.
The main.js file has a hardcoded AES-256-CBC key and IV at the top, anti-VM GPU check targeting Hyper-V and Basic Display adapters, and the PowerShell Add-MpPreference exclusion command.
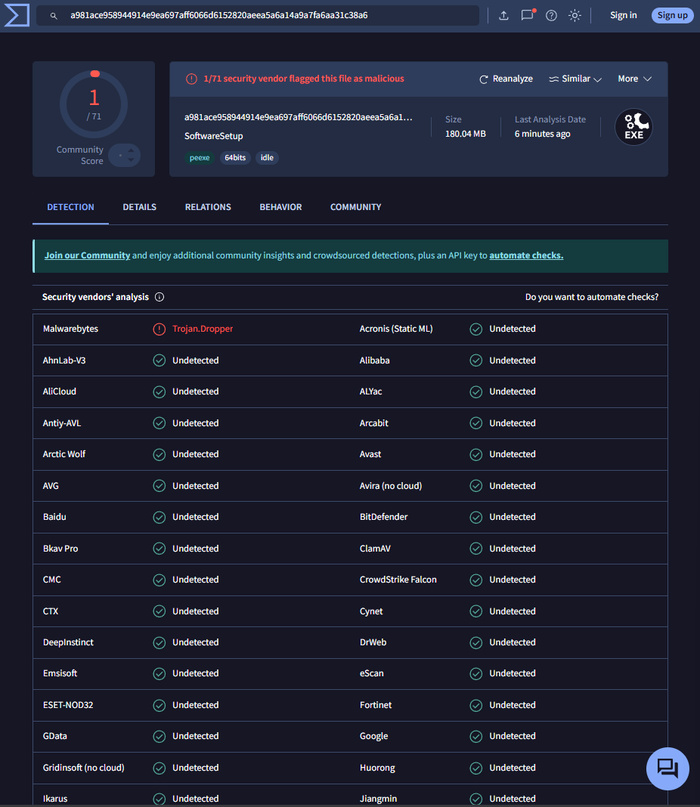
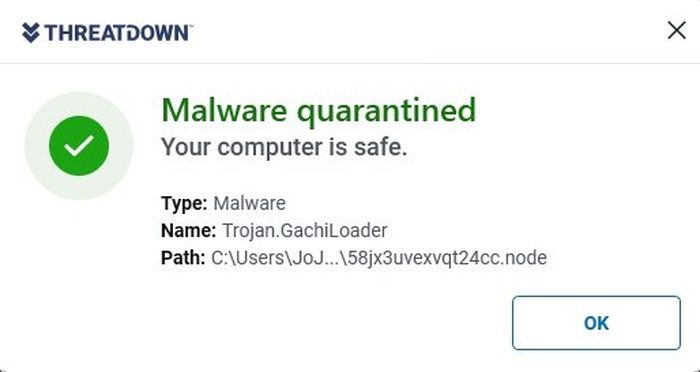
Threat actors frequently use Electron packaging to evade detection. As the VirusTotal screenshot shows, this technique is quite effective, with very low detection rates among major antivirus products. At the time of writing, only ThreatDown’s Malwarebytes engine detects the Electron executable.
Conclusion
This campaign marks a deliberate shift in GachiLoader’s playbook. By weaponizing the AI agent skill format, threat actors have found a new effective initial access vector that security tools are not yet built to scrutinize. As AI agent ecosystems expand, so does the attack surface they introduce.
Skills are the new phishing attachment.
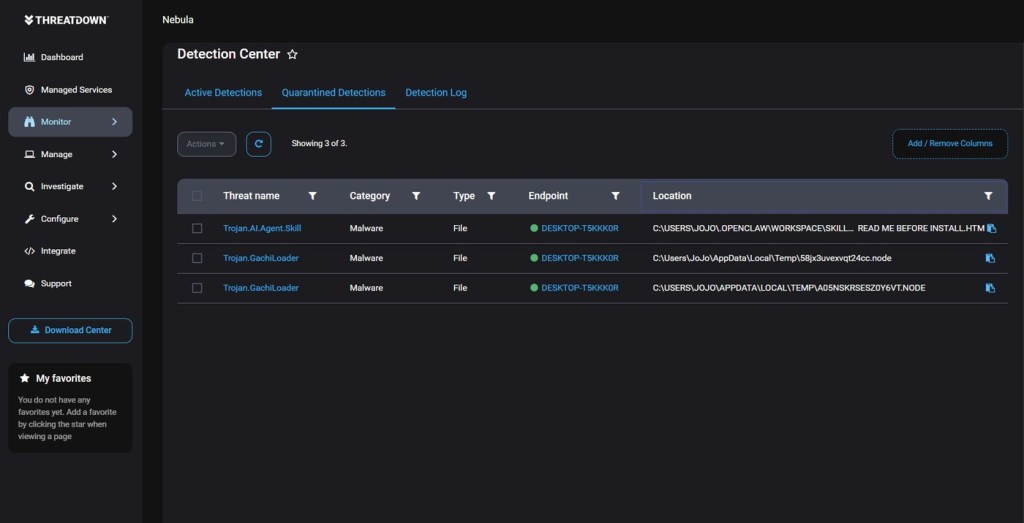
ThreatDown detections
ThreatDown Endpoint Protection detects this threat family. Real-Time Protection blocks payload execution and network connections.
Indicators of Compromise
| Indicator | Type | Description |
|---|---|---|
| 076ba40e7fbf2910dff87f0c25862a70001d8ad81d23d8beae9fb9b29b603829 | SHA-256 | OpenClaw Polymarket-Trade skill |
| f583f8307468dc5eacc7be7137dc5c7dbab5fc30ca89b03cf6c67b4de030b05d | SHA-256 | OpenClaw Polymarket Electron dropper |
| a981ace958944914e9ea697aff6066d6152820aeea5a6a14a9a7fa6aa31c38a6 | SHA-256 | Main Electron executable |
| 8abec84db36ee18b3299b5fd9406f8d99a5be7dd0a4e93536e39bb406fce97a6 | SHA-256 | Libs_Installer (Node SEA) |
| 1753d2f90bd4ac6c0c91e76322ae1d0cc8034842a61dc175c7aba3e1aa944c90 | SHA-256 | Required_libs (Node SEA) |
| 539ac28b816ed0ab17879712a460396bd812221b93540590eccdb89c8196db96 | SHA-256 | GachiLoader |
| 9fb2ea25254ae53f93e0e13abb59a76a6c1ed512cdf1c1deafafa4d2758117f6 | SHA-256 | GachiLoader |
| 1831db8fe19efbd12997f63bc76da79858f87995b9ebd8a05757670e5e52c1f2 | SHA-256 | GachiLoader |
| %TEMP%\*.node | File path | Randomly named .node executables dropped in %TEMP% |
| 1f24e75c1e6d6777e970f64ebf18e8bf1dd1dcaab692adf4062c8fad6a6df42c | SHA-256 | Rhadamanthys infostealer |
| *.onfinality[.]pro | Domain | GachiLoader C2 (resolved via Polygon smart contract) |
| 0x519b925A40b29D879d751A99F280006bC0f4EF69 | Smart contract | Polygon blockchain contract used as C2 resolver |
| https://github[.]com/blueberywoodsym/openclawlibs | URL | GitHub distribution infrastructure |
Cybercrime Has Gone Machine-Scale
AI is automating malware faster than security can adapt.
Get the facts Read the 2026 State of MalwareCybercrime Has Gone Machine-Scale
AI is automating malware faster than security can adapt.
Get the facts Read the 2026 State of Malware


