
ION starts bringing customers back online after LockBit ransomware attack
Pernicious ransomware group, LockBit, is making headlines again. Less than a month after attacking HACLA, it hit the derivative trading division of ION Group, a financial software company.
ION Group, a financial software firm, is reportedly beginning to bring clients back online after being hit by a ransomware attack late last week.
The Russian-linked LockBit ransomware group claimed responsibility for attacking a division of ION Group, which affecting 42 clients in Europe and the United States. The incident forced several banks and brokers to process trades manually.
The subsidiary, ION Cleared Derivatives, which offers software for automating the trading cycle and the clearing process for derivatives, released a very short statement regarding the “cybersecurity event” on Tuesday.
The incident is contained to a specific environment, all the affected servers are disconnected, and remediation of services is ongoing. Further updates will be posted when available.
In a statement last week, Deputy Assistant Secretary of the Treasury’s Office of Cybersecurity and Critical Infrastructure Protection Todd Conklin was quoted saying the disruption to Cleared Derivatives’ platform does not pose a “systemic risk to the financial sector”, adding that the incident is isolated to a small number of smaller and mid-size firms. “We remain connected with key financial sector partners, and will advise of any changes to this assessment,” he further said.
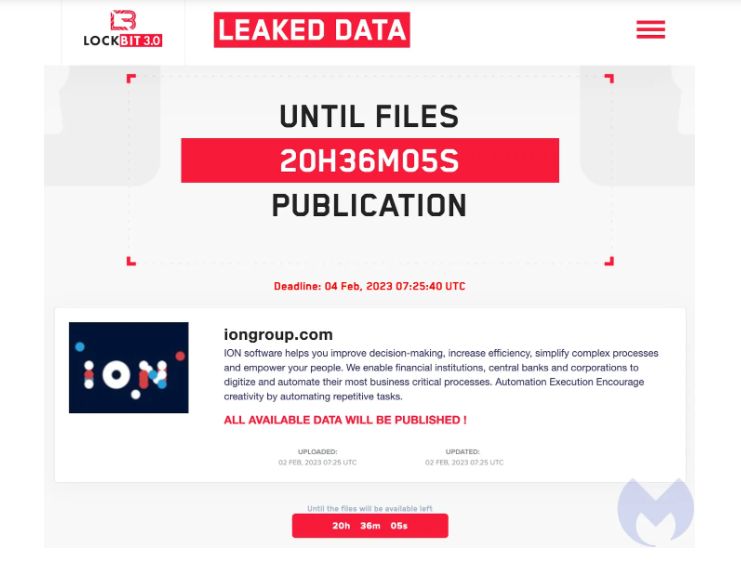
The ION Group leak site post (Source: Malwarebytes)
On Friday, February 4, the ransomware group claimed the ransom had been paid, with Reuters quoting the attackers as saying the money was paid by a “very rich unknown philanthropist”. Both ION and LockBit declined to reveal further details.
In an interview with The Register, Tom Kellermann, senior VP of cyber strategy at Contrast said that supply chain attacks like this are becoming common in the financial sector. “Shared service providers are being increasingly targeted by cybercrime cartels to manifest island hopping,” he said. “Cyberattacks in the financial sector are no longer merely about conducting a heist but rather to hijack the digital transformation of the victim so as to launch attacks against their customer base.”
Last month, the LockBit ransomware group attacked Royal Mail during the first week and the Housing Authority of the City of Los Angeles (HACLA) just days after.
How to avoid ransomware
There is no doubt hospitals remain under a bullseye, and attackers can strike at any time. Thankfully, there are ways organizations can help reduce their risk of suffering from a ransomware attack.
- Have an incident response (IR) plan. Organizations should accept the fact that a cyberattack is likely to affect them at some point, whether they’re the direct victim or part of a supply chain. An IR plan can direct your responders on what to do in the event of a cybersecurity attack. This should include restoring from backups, client outreach, and reporting to law enforcement among others.
- Educate your staff. Awareness goes a long way, and everyone in the company has a responsibility to keep the organization’s network safe. Staff should be taught social engineering tactics and red flags of a system attack, so they can alert the right personnel quickly should an attack occur.
- Patch as soon as you can. Many threat actors get into networks by exploiting unpatched vulnerabilities. Have a patching plan in place to ensure that your organization’s network is protected against the latest and most exploited weaknesses.
- Backup your files. Backups have saved a lot of organizations after a ransomware attack—provided they work. When you make a plan, ensure you also have provisions for backup testing.
- Get an EDR solution. ThreatDown Endpoint Detection and Response offers built-in ransomware protection, 72-hour ransomware rollback, and zero-day ransomware protection.
Stay safe!
Cybercrime Has Gone Machine-Scale
AI is automating malware faster than security can adapt.
Get the facts Read the 2026 State of MalwareCybercrime Has Gone Machine-Scale
AI is automating malware faster than security can adapt.
Get the facts Read the 2026 State of Malware


