Threat Intelligence
Lazarus APT conceals malicious code within BMP image to drop its RAT
Threat Intelligence Team
9 minutes
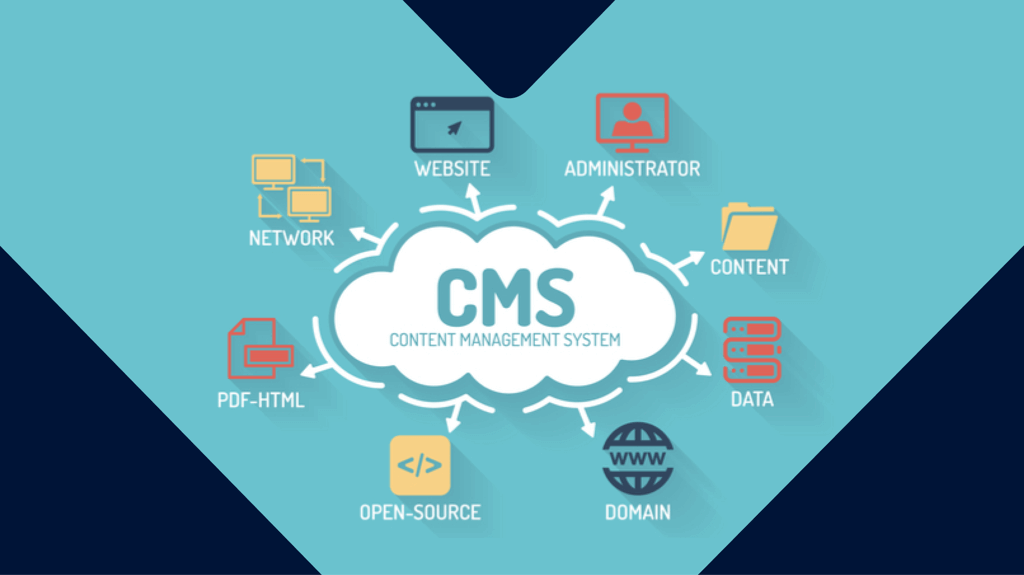
How to secure your content management system
Popular content management systems are easy to install and use. But how easy is it to keep them secure?
4 minutes
Cybercrime Has Gone Machine-Scale
AI is automating malware faster than security can adapt.
Get the facts Read the 2026 State of Malware